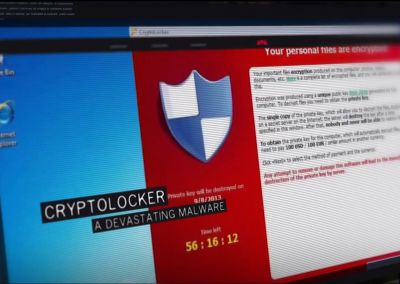
Photo Credit: Christiaan Colen – Flickr
This video looks at a phishing operation in Brazil that hosted phishing site templates, malware, and victims’ personal documents in an online sharing site.
This attack was also used during the World Cup 2014 to lure victims into clicking malicious links.