The Chaos Communication Congress is an annual meeting of the international hacker scene, organised by the Chaos Computer Club.
The Congress offers lectures and workshops and various events on a multitude of topics including (but not limited to) information technology and generally a critical-creative attitude towards technology and the discussion about the effects of technological advances on society.
Conference information
Days until the next conference
Day(s)
:
Hour(s)
:
Minute(s)
:
Second(s)
Location
Congress Center Hamburg
Am Dammtor / Marseiller Strasse
20355 Hamburg
Germany
Conference program
The conference program can be viewed here.
CCH - Congress Center Hamburg
Articles
How secure is your security badge?
14-08-2014 | Nearly four years ago, researchers at the Chaos Communication Congress (CCC), a security conference in Berlin, released a paper (PDF) demonstrating a serious vulnerability in smart cards made by Austin, Texas-based HID Global, by far the largest manufacturer of these devices. The CCC researchers showed that the card reader device that HID sells to validate the data stored on its then-new line of iClass proximity cards includes the master encryption key needed to read data on those cards. Read more
Cash machines raided with infected USB sticks
30-12-2013 | Researchers have revealed how cyber-thieves sliced into cash machines in order to infect them with malware earlier this year. The criminals cut the holes in order to plug in USB drives that installed their code onto the ATMs. Details of the attacks on an unnamed European bank’s cash dispensers were presented at the hacker-themed Chaos Communication Congress in Hamburg. Read more
WikiLeaks’ Julian Assange calls on computer hackers to unite against NSA surveillance
31-12-2013 | WikiLeaks founder Julian Assange addressed a major gathering of computer experts Monday at the Chaos Communication Congress in Hamburg, Germany, calling on them to join forces in resisting government intrusions on Internet freedom and privacy. Read more
Flash memory cards contain powerful, unsecured microcontrollers
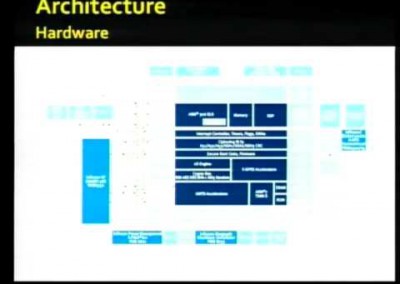
31-12-2013 | Researchers demonstrated yesterday at the Chaos Communication Congress in Hamburg that they could write arbitrary code onto various SD memory cards, a hack that could give attackers the ability to perform man-in-the-middle attacks on devices housing the cards, as well as give users access to an inexpensive source of powerful and programmable microcontrollers. Read more
Available playlists
30C3
(only English)
30C3
(only German)
29C3: Not my department
(only English)
29C3: Not my department
(only German)
28C3: Behind Enemy Lines
(only English)
28C3: Behind Enemy Lines
(only German)