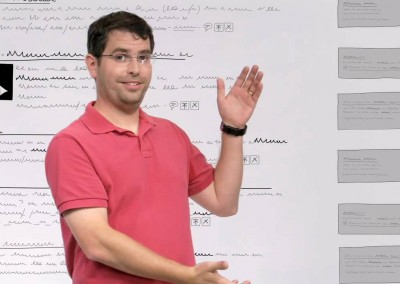
Photo Credit: Pranav Mistry – Wikimedia Commons
At TEDIndia, Pranav Mistry demos several tools that help the physical world interact with the world of data.
Including a deep look at his SixthSense device and a new, paradigm-shifting paper “laptop.”
At TEDIndia, Pranav Mistry demos several tools that help the physical world interact with the world of data.
Including a deep look at his SixthSense device and a new, paradigm-shifting paper “laptop.”