How we take back the Internet
Photo Credit: TED Conference – Flickr
Appearing by telepresence robot Edward Snowden speaks at TED2014 about surveillance and Internet freedom.
The right to data privacy, requires a fundamental rethink of the role of the internet in our lives and the laws that protect it.
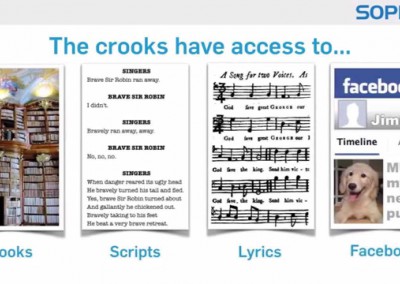
Related videos
Related videos
Videos from the same category or videos related to the subject.
You will find something new to watch and expand your knowledge.