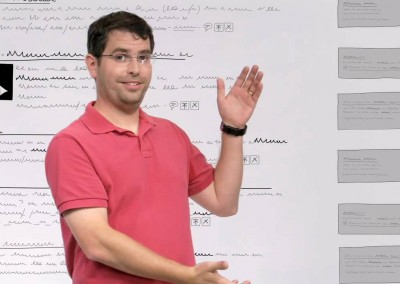
Photo Credit: TED Conference – Flickr
Ever wonder who controls the inner workings of the Internet? Like what happens after you type in a URL and hit enter, or who assigns IP addresses?
Vint Cerf is here to explain.
Ever wonder who controls the inner workings of the Internet? Like what happens after you type in a URL and hit enter, or who assigns IP addresses?
Vint Cerf is here to explain.