Photo Credit: Aurélie Jouan – StockSnap.io
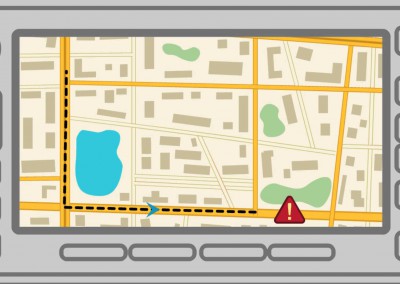
More and more cities are adopting a modern approach to consuming and distributing power via smart meters and smart grids.
Trend Micro explains how the advancement of meters and grids can lead to a smarter energy future and expose the many security issues.
More and more cities are adopting a modern approach to consuming and distributing power via smart meters and smart grids.
Trend Micro explains how the advancement of meters and grids can lead to a smarter energy future and expose the many security issues.