Photo Credit: Christiaan Colen – Flickr
While researching into how secure printers are, Ben Smith discovered some new malicious abuses as well as some fun new uses for old attacks.
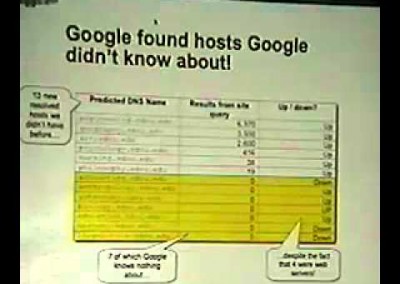
This talk will cover how to send SNMP commands to HP printers and get back responses even if SNMP is disabled on the device.
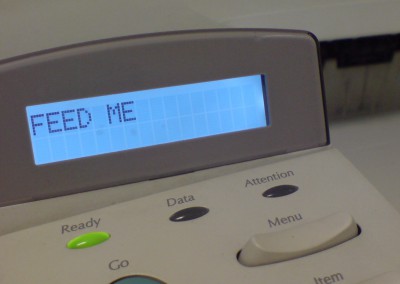
As well as discus some of the other fun that can be had with PJL and its lack of security like printer information gathering, control panel lockout, disk lockout, file uploads, file downloads and mass LCD changing.
While researching into how secure printers are, Ben Smith discovered some new malicious abuses as well as some fun new uses for old attacks.
This talk will cover how to send SNMP commands to HP printers and get back responses even if SNMP is disabled on the device.
As well as discus some of the other fun that can be had with PJL and its lack of security like printer information gathering, control panel lockout, disk lockout, file uploads, file downloads and mass LCD changing.
About the speaker
Security architect / Researcher. Author of several security tools, and one book. In my free time I work on various security projects. Some are RF/Wireless related, others, are not.
Specialties: Wireless, Member of Aircrack-ng team. Networking. Creative Problem Solving.
Connect
About the speaker
Security architect / Researcher. Author of several security tools, and one book. In my free time I work on various security projects. Some are RF/Wireless related, others, are not.
Specialties: Wireless, Member of Aircrack-ng team. Networking. Creative Problem Solving.

Resources
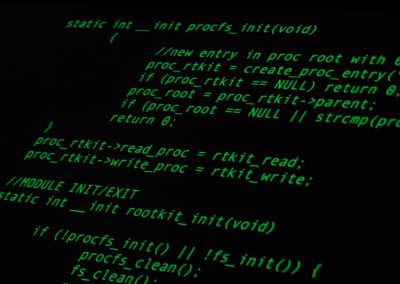
During the 28th Chaos Communication Congress Ang Cui and Jonathan Voris present several generic firmware modification attacks against HP printers.
The attacks they present exploit a functional vulnerability common to all HP printers, and do not depend on any specific code vulnerability.
Update anyone’s printer with a Trojan image which spies on the documents being printed
The hacking possibilities go far beyond enabling choppy, early ’90s gaming: “We can therefore create our own custom firmware and update anyone’s printer with a Trojan image which spies on the documents being printed or is used as a gateway into their network” Jordon wrote. Read more
When firmware modifications attack: A case study of embedded exploitation
We present a case study of the HP-RFU (Remote Firmware Update) LaserJet printer firmware modification vulnerability, which allows arbitrary injection of malware into the printer’s firmware via standard printed documents. Read more
Utterly crazy hack uses long-distance lasers to send malware commands via all-in-one printers
Researchers found that if a multifunction printer is attached to an air-gapped computer, attackers could issue commands to a malicious program running on it by flashing visible or infrared light at the scanner lid when open. Read more
Resources
During the 28th Chaos Communication Congress Ang Cui and Jonathan Voris present several generic firmware modification attacks against HP printers.
The attacks they present exploit a functional vulnerability common to all HP printers, and do not depend on any specific code vulnerability.
Update anyone’s printer with a Trojan image which spies on the documents being printed
The hacking possibilities go far beyond enabling choppy, early ’90s gaming: “We can therefore create our own custom firmware and update anyone’s printer with a Trojan image which spies on the documents being printed or is used as a gateway into their network” Jordon wrote. Read more
When firmware modifications attack: A case study of embedded exploitation
We present a case study of the HP-RFU (Remote Firmware Update) LaserJet printer firmware modification vulnerability, which allows arbitrary injection of malware into the printer’s firmware via standard printed documents. Read more
Utterly crazy hack uses long-distance lasers to send malware commands via all-in-one printers
Researchers found that if a multifunction printer is attached to an air-gapped computer, attackers could issue commands to a malicious program running on it by flashing visible or infrared light at the scanner lid when open. Read more
Articles
HP Printer security flaw allows hackers to extract passwords
Date: 07-08-2013
Source: Graham Cluley
The hidden IT security threat: Multifunction printers
Date: 07-02-2013
Source: Forbes
Best practices for printer security
Date: 26-07-2012
Source: Networkworld
Hacking attacks on printers still not being taken seriously
Date: 23-07-2012
Source: The Guardian
Your printer could be a security sore spot
Date: 25-04-2012
Source: PCWorld
Tens of millions of HP LaserJet printers vulnerable to remote hacking
Date: 29-11-2011
Source: ExtremeTech
Shmoocon 2011 conference wrap-up
Date: 01-02-2011
Source: Tenable
Presentations
Attacking networked embedded systems
Date: 02-08-2002
Source: Phenoelit
Hacking printers: for fun, profit and (anti)warfare
Date: 2011
Source: Andrei Costin
Hacking printers: 10 years down the road
Date: 2011
Source: Andrei Costin
Exploiting printers by analysing their firmware
Date: 20-11-2009
Source: YouTube
Tutorials
Making your printer say "Feed Me a Kitten" and also exfiltrate sensitive data
Date: 24-01-2014
Source: Rapid7
“Hacking” printers - PJL basics
Date: 01-12-2011
Source: Hacking on a dime
Hacking network printers
Date: 11-09-2005
Source: Irongeek